Malicious hackers wasted no time exploiting a critical bug in the Drupal content management system that allows them to execute malicious code on website servers. Vintage wine region maps. Just hours after maintainers of the open-source program disclosed the vulnerability, it came under active attack, they said.
Notice: Array to string conversion in themebibliotabular (line 244 of /home/www/drupal-7.59/sites/all/modules/biblio/includes/bibliotheme.inc. Drupal 7.x 7.59 Remote Code Execution Vulnerability Description According to its self-reported version number, the detected Drupal application is affected by a remote code execution vulnerability. Note that the scanner has not tested for these issues but has instead. This is the 32rd tutorial in the Drupal 7 tutorial series. This tutorial shows you how to update the core version of Drupal 7. Subscribe for more free tutori.

Participate in discussions with other Treehouse members and learn. Viscosity Solution of Second Order HJI Equation and Application to Zero-Sum Stochastic Differential Game.
So far, the attackers are using proof-of-concept attack code published online that shows one method of exploiting the critical flaw, Drupal security team member Greg Knaddison told Ars. The code has not yet been automated in a way that can target large numbers of sites, in large part because successful exploits require permissions and configuration settings that differ from site to site. So far, Drupal maintainers aren't aware of any successful site take-overs resulting from the vulnerability.
'We have definitely seen proof of concept exploits published online,' Knaddison wrote in an e-mail. 'It's safe to assume that proof of concept (or others like it) are being used maliciously against individual sites by people who are willing to slowly attack a high value target. It's not yet automated in a way that would let an attacker try it against hundreds of sites.'
Now that the vulnerability is actively being exploited maintainers have raised the severity rating to highly critical. Reaper mp3. Previously, the rating was critical. What follows is the post as it was published at 12:24 PM California time, prior to Drupal maintainers' update.
For the second time in a month, websites that use the Drupal content management system are confronted with a stark choice: install a critical update or risk having your servers infected with ransomware or other nasties.
AdvertisementMaintainers of the open-source CMS built on the PHP programming language released an update patching critical remote-code vulnerability on Wednesday. The bug, formally indexed as CVE-2018-7602, exists within multiple subsystems of Drupal 7.x and 8.x. Drupal maintainers didn't provide details on how the vulnerability can be exploited other than to say that attacks work remotely. The maintainers rated the vulnerability 'critical' and urged websites to patch it as soon as possible.
That severity rating is one notch lower than the so-called 'Drupalgeddon2' bug maintainers patched late last month. Formally indexed as CVE-2018-7600, that bug also made it possible for attackers to remotely execute code of their choice on vulnerable servers, in that case simply by accessing a URL and injecting exploit code. That issue became public shortly after the patch was released. Since then, multiple attack groups have been actively exploiting the critical flaw to install cryptocurrency miners and malware that performs denial-of-service attacks on other servers.Among those attacks, malicious hackers recently exploited Drupalgeddon2 to install ransomware on servers that run the website for the Ukrainian Ministry of Energy, Threatpost reported Tuesday. Security researcher Troy Mursch told Ars the report was credible and cited this Web archive of the site, which showed the Ukrainian government site was vulnerable as recently as April 19.
The severity of the Drupal bug patched Wednesday is lower because it's 'more complex to exploit and requires more permissions on the site' than the Drupalgeddon2 exploits, a Drupal maintainer told Ars. Maintainers rate the risk of CVE-2018-7602 as 17 out of 25, compared with a 21 out of 25 for Drupalgeddon2 when it was first disclosed. Chime login amazon. Maintainers are currently unaware of any active exploits of the newly revealed CVE-2018-7602, but despite increased challenges, it wouldn't be surprising to see that situation change.
Websites that are running Drupal 7.x should immediately upgrade to Drupal 7.59. Those running 8.5.x should upgrade to 8.5.3. Normally, maintainers don't provide patches for 8.4.x, but they have made an exception in this case. Those websites should upgrade to 8.4.8 and then to 8.5.3 or the latest secure release.
[Note] Open Atrium (a Drupal distribution) and CiviCRM (CMS integration with Drupal) are also affected by this vulnerability. Make sure that your deployment is updated to the latest version.Drupal has released a new version that fixes a highly critical security vulnerability. We strongly recommend upgrading your existing Drupal 7 and 8 sites.
A remote code execution vulnerability exists within multiple subsystems of Drupal 7.x and 8.x. This potentially allows attackers to exploit multiple attack vectors on a Drupal site, which could result in the site being completely compromised. This vulnerability is related to Drupal core - Highly critical - Remote Code Execution - SA-CORE-2018-002. Both SA-CORE-2018-002 and this vulnerability are being exploited in the wild.
It is recommended that you upgrade your Drupal application to Drupal 7.59 or later and Drupal 8.5.3 or later. We highly recommend creating a backup before proceeding. You can follow our documentation to learn how to upgrade your application and ensure its security.
If you are unable to update immediately and have advanced Drupal administration skills, you may opt to patch your systems until such time as you are able to completely update. The Drupal community has provided patches which can be applied using the following procedure:
1. Move to Drupal directory (assuming /opt/bitnami/ as installdir):
Drupal 7.69 Download
cd /opt/bitnami/apps/drupal/htdocs/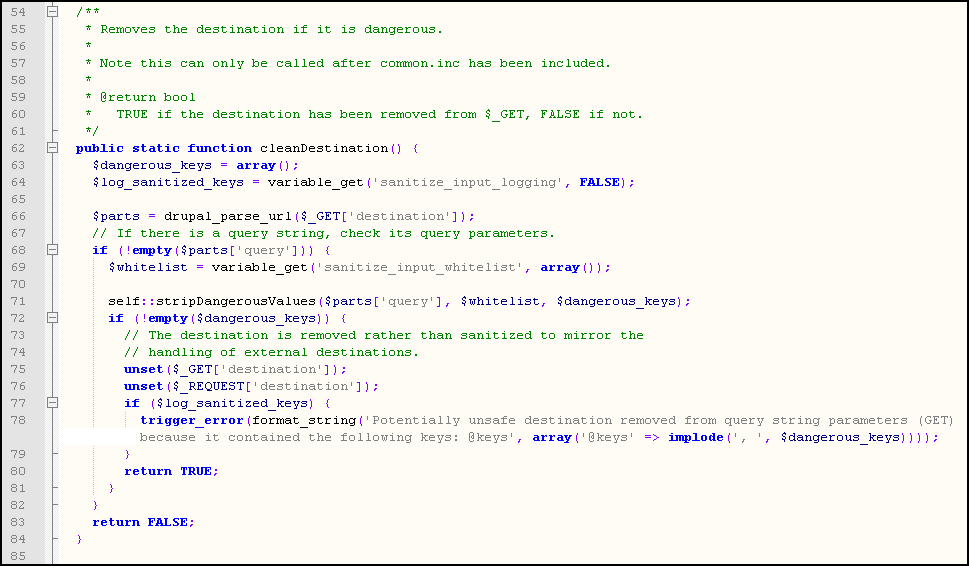
Participate in discussions with other Treehouse members and learn. Viscosity Solution of Second Order HJI Equation and Application to Zero-Sum Stochastic Differential Game.
So far, the attackers are using proof-of-concept attack code published online that shows one method of exploiting the critical flaw, Drupal security team member Greg Knaddison told Ars. The code has not yet been automated in a way that can target large numbers of sites, in large part because successful exploits require permissions and configuration settings that differ from site to site. So far, Drupal maintainers aren't aware of any successful site take-overs resulting from the vulnerability.
'We have definitely seen proof of concept exploits published online,' Knaddison wrote in an e-mail. 'It's safe to assume that proof of concept (or others like it) are being used maliciously against individual sites by people who are willing to slowly attack a high value target. It's not yet automated in a way that would let an attacker try it against hundreds of sites.'
Now that the vulnerability is actively being exploited maintainers have raised the severity rating to highly critical. Reaper mp3. Previously, the rating was critical. What follows is the post as it was published at 12:24 PM California time, prior to Drupal maintainers' update.
For the second time in a month, websites that use the Drupal content management system are confronted with a stark choice: install a critical update or risk having your servers infected with ransomware or other nasties.
AdvertisementMaintainers of the open-source CMS built on the PHP programming language released an update patching critical remote-code vulnerability on Wednesday. The bug, formally indexed as CVE-2018-7602, exists within multiple subsystems of Drupal 7.x and 8.x. Drupal maintainers didn't provide details on how the vulnerability can be exploited other than to say that attacks work remotely. The maintainers rated the vulnerability 'critical' and urged websites to patch it as soon as possible.
That severity rating is one notch lower than the so-called 'Drupalgeddon2' bug maintainers patched late last month. Formally indexed as CVE-2018-7600, that bug also made it possible for attackers to remotely execute code of their choice on vulnerable servers, in that case simply by accessing a URL and injecting exploit code. That issue became public shortly after the patch was released. Since then, multiple attack groups have been actively exploiting the critical flaw to install cryptocurrency miners and malware that performs denial-of-service attacks on other servers.Among those attacks, malicious hackers recently exploited Drupalgeddon2 to install ransomware on servers that run the website for the Ukrainian Ministry of Energy, Threatpost reported Tuesday. Security researcher Troy Mursch told Ars the report was credible and cited this Web archive of the site, which showed the Ukrainian government site was vulnerable as recently as April 19.
The severity of the Drupal bug patched Wednesday is lower because it's 'more complex to exploit and requires more permissions on the site' than the Drupalgeddon2 exploits, a Drupal maintainer told Ars. Maintainers rate the risk of CVE-2018-7602 as 17 out of 25, compared with a 21 out of 25 for Drupalgeddon2 when it was first disclosed. Chime login amazon. Maintainers are currently unaware of any active exploits of the newly revealed CVE-2018-7602, but despite increased challenges, it wouldn't be surprising to see that situation change.
Websites that are running Drupal 7.x should immediately upgrade to Drupal 7.59. Those running 8.5.x should upgrade to 8.5.3. Normally, maintainers don't provide patches for 8.4.x, but they have made an exception in this case. Those websites should upgrade to 8.4.8 and then to 8.5.3 or the latest secure release.
[Note] Open Atrium (a Drupal distribution) and CiviCRM (CMS integration with Drupal) are also affected by this vulnerability. Make sure that your deployment is updated to the latest version.Drupal has released a new version that fixes a highly critical security vulnerability. We strongly recommend upgrading your existing Drupal 7 and 8 sites.
A remote code execution vulnerability exists within multiple subsystems of Drupal 7.x and 8.x. This potentially allows attackers to exploit multiple attack vectors on a Drupal site, which could result in the site being completely compromised. This vulnerability is related to Drupal core - Highly critical - Remote Code Execution - SA-CORE-2018-002. Both SA-CORE-2018-002 and this vulnerability are being exploited in the wild.
It is recommended that you upgrade your Drupal application to Drupal 7.59 or later and Drupal 8.5.3 or later. We highly recommend creating a backup before proceeding. You can follow our documentation to learn how to upgrade your application and ensure its security.
If you are unable to update immediately and have advanced Drupal administration skills, you may opt to patch your systems until such time as you are able to completely update. The Drupal community has provided patches which can be applied using the following procedure:
1. Move to Drupal directory (assuming /opt/bitnami/ as installdir):
Drupal 7.69 Download
cd /opt/bitnami/apps/drupal/htdocs/2. Download the correct patch for your system based on the version of Drupal in use.
- For Drupal 7.x:
wget -O drupal.patch 'https://cgit.drupalcode.org/drupal/rawdiff/?h=7.x&id=080daa38f265ea28444c540832509a48861587d0'
wget -O drupal.patch 'https://cgit.drupalcode.org/drupal/rawdiff/?h=8.5.x&id=bb6d396609600d1169da29456ba3db59abae4b7e'
Drupal 7.69
For new application deployments, including the Bitnami Launchpad, we are releasing Drupal 7.59 and 8.5.3 containers, installers, virtual machines and cloud images that include the fix to address this vulnerability. If you deploy Bitnami Drupal and it is not yet updated to its latest version, you will need to upgrade by following our documentation.
If you have further questions about Bitnami Drupal or this security issue, please post to our community forum, where we will be happy to help.

